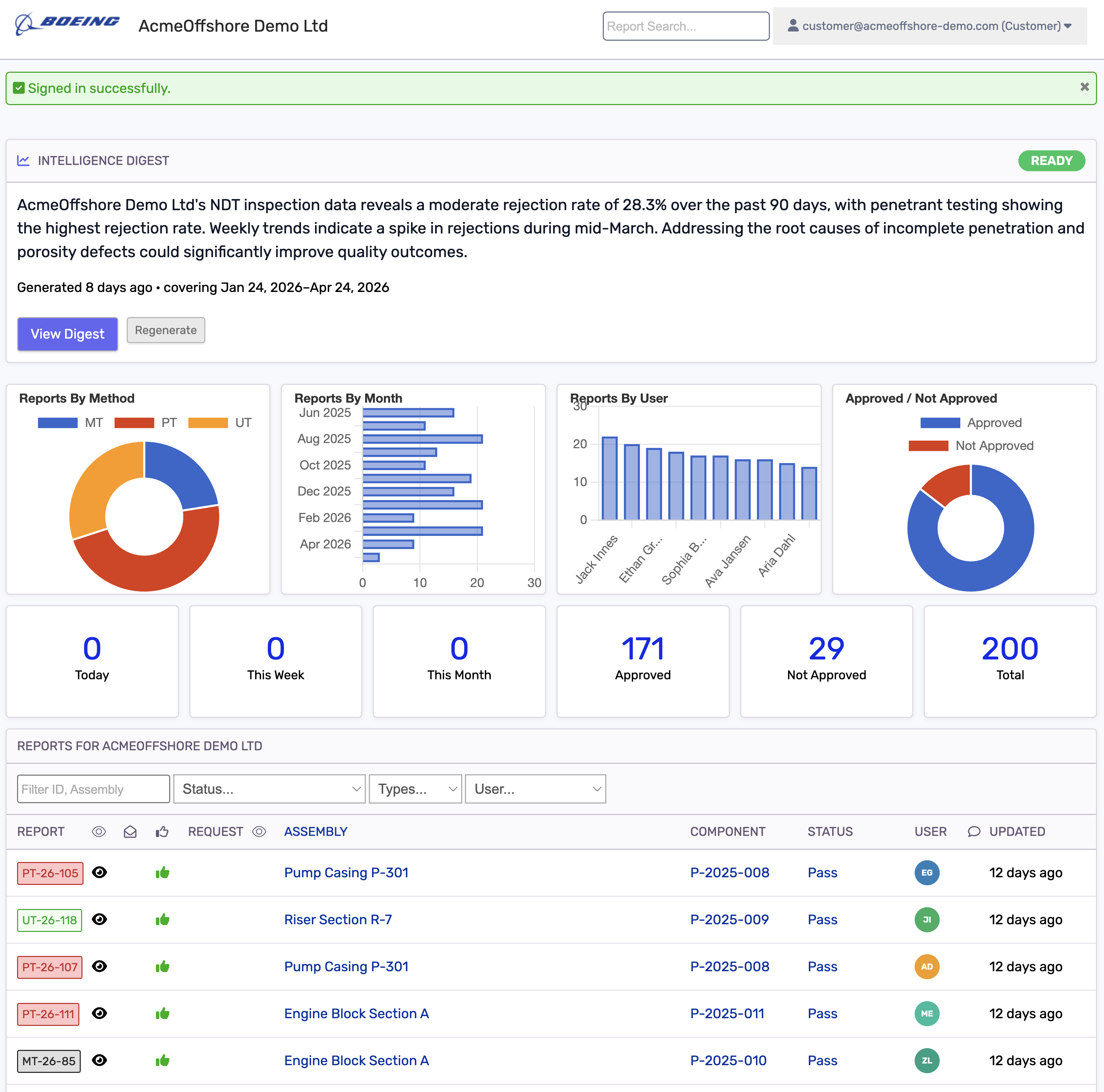
Information Security Management
Supports controlled access, secure cloud hosting, user permissions, and protected report archives so inspection data is managed with clear accountability.
- Role-based access controls
- Secure report archive
- User activity history
- Controlled client access